Bonded Internet scalability and security lets you build alternative WAN solutions for Enterprise clients.
With Bonded Internet, creating a hosted and hosted-hybrid WAN for clients is easy. Ask us how, we’d be happy to show you.
Improve uptime
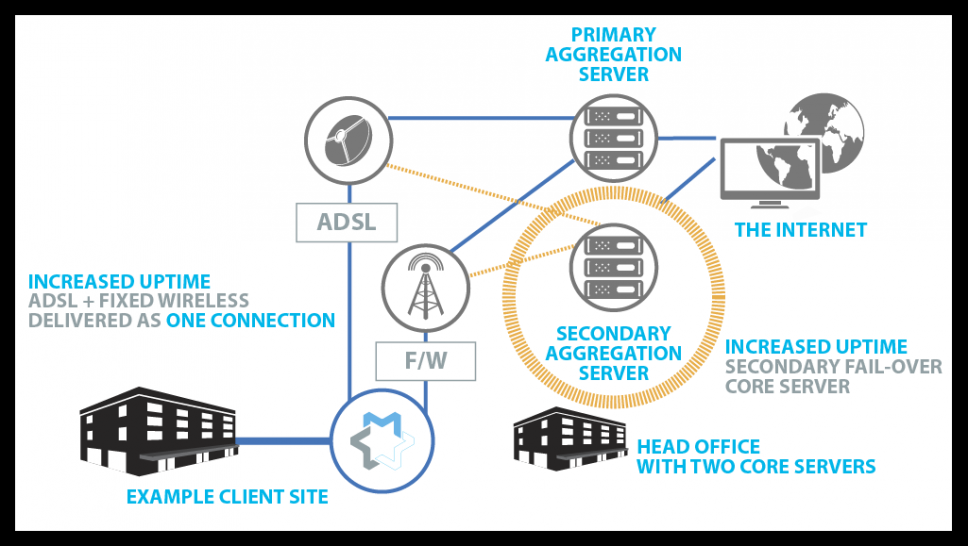
Maintaining network availability is easy with Bonded Internet. Delivering multiple broadband connections as one bonded IP access circuit means you can sell on-net and off-net connections, but maintain control and management over the clients’ network. Bonded Internet creates a proprietary bonded tunnel made up of multiple connections – the IP address on the client gateway, however, is yours – whether the circuits are or not. Mixing and matching connections makes it less likely that your clients will have to rely on the uptime of a single provider.
Protecting the Core
More than just client-side redundancy, Multapplied’s Bonded Internet service comes equipped to handle core-redundancy. All sites connect to the client Head Office where traffic is controlled and where the bonding “magic” happens. The core device can be duplicated and set as a fail-over device in the event of a hardware issue. If the client wants increased uptime, we suggest setting up the failover device outside the client’s Head Office so they’re doubly protected.
Quadruple Security
Doubling the protection in the core is just one way of increasing uptime. But Bonded Internet comes (out-of-the-box) equipped with four distinct levels of security to ensure traffic passed over the Enterprise WAN isn’t compromised.
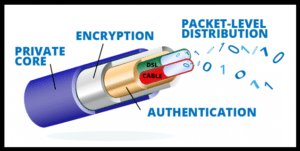
1. Packet Level Distribution
At the packet-level, data is distributed between the multiple connections used to create the bond. It’s an algorithm we’ve created internally that drives how much data is passed over which connection, but it protects your client in the sense that any compromised connection won’t be carrying the entire transmission – making it nearly impossible to decipher the data.
2. Authentication
Clearly, for Bonded Internet to work, it requires for both ends (the Client-side device (CPE) and the Core Server (Aggregator)) to communicate. This communication is first handled through an authentication “hand-shake” that allows for the devices to speak to each other.
3. Encryption
Bonded Internet comes with Three flavours of encryption to further secure your clients’ traffic. Site-to-Site and Site-to-Multisite IPVPNs can be created using AES and SALSA Encryption methodologies and is all managed through our simple-to-navigate user interface.
4. Private Core Routers
Because our partners are given unlimited aggregation server licenses, they can install servers easily and affordably at their clients’ sites so that the client isn’t sharing any CPU or Memory with any other clients. The private core routers (Aggregators) sit behind the client’s firewall and are monitored and managed by our partners.
For more information on Bonded Internet and how you can create an affordable Enterprise WAN, please contact us.
Are you an enterprise looking for an alternative to MPLS?
Contact us and we’ll be happy to show you a demonstration of how the technology works, and where you can find one of our Global partners to set up your own system and manage it for you.

